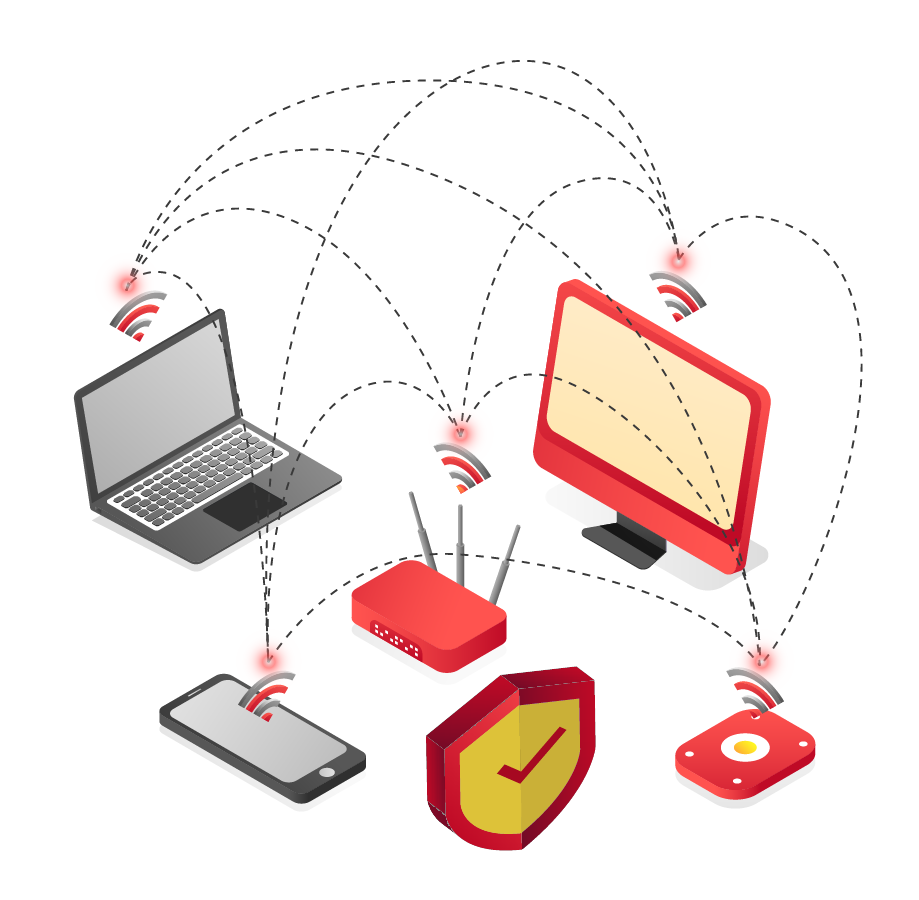
What is Wireless Penetration Test?
A Wireless Penetration test is an approved assessment exercise, which is intended to identify vulnerabilities in security controls utilized by various wireless technologies and standards, misconfigured access points, and weak security protocols. A lot of cooperates setup an an unencrypted “guest” WiFi network and connect it to the internet. While the plurality of these sorts of network are considered to be okay by their extremely nature, but they can present various potential attack vectors:
- If separation within wireless network has not been enough in place, then network sniffing and man-in-the-middle attack can easy be inconsequentially actualized.
- Older devices can bring more risks by connecting unencrypted WiFi connections and wired network at the same time.
- Internal threats can potentially be an attack vector to the endpoints themselves such as the connected devices in the same WiFi.
What You Get!
The result of a wireless test is a detailed report with a guide which clarifies what safeguards ought to be taken at different physical access points. RedForce Networks has performed such testing for different customers who needed to shield their mission critical infrastructure from prying eyes, using wireless signals.
Benefits to Your Business!
Guarantee Compliance with well-known security guideline like PCI-DSS and ISO 27001.
Review security checking methods and incident response strategies.
Identify vulnerabilities, misconfigured wireless devices, and rogue access points.
Decrease the security risk of legal implications of a business breach.
Hardening the remote access way to your interior network.
Get autonomous security check – of encryption and validation authentication policies – for devices collaborating with your wireless network.
Deny access as a pivot for cyber attacks by unauthorized use of your wireless network, which might be followed back to your cooperate.
Give administration a proof of exploit, which plots the advantages that an exploit can compromise; for example, compromising critical data or gaining administrative level rights over routers and switches.
